OpenClaw Ops — Bikin Gateway Kamu Self-Healing Setelah Update

OpenClaw Ops — Bikin Gateway Kamu Self-Healing
Gue benci momen ini.
Besok bangun, buka Telegram — agents pada diam. Cek server — gateway down. Cek logs — auth error. Cek exec approval — nge-blok semua command.
Penyebabnya? Update OpenClaw semalam.
Ini bukan overheal. Ini pola yang konsisten. OpenClaw aggressive soal update, dan tiap update selalu ada yang ke-reset: auth mode, exec policy, allowlist, cron job. Lo gak notice sampai sesuatu penting udah kelewat.
Cathryn Lavery build openclaw-ops — skill yang ngurus semua itu secara otomatis. Auto-fix, auto-restart, auto-log.
Bridged to Sumopod VPS
This openclaw-ops setup runs natively on Sumopod VPS — a managed OpenClaw hosting service built on Alibaba Cloud ECS.
Architecture:
- Gateway deployed on Sumopod VPS (Intel Xeon, 2 vCPU, 8GB RAM)
- Health checks run every 5 minutes via cron
- Alerts sent to Telegram when issues detected
- Auto-repair scripts execute automatically
Learn more about Sumopod VPS: https://blog.fanani.co/sumopod
Kenapa Ini Perlu?
Oke jadi singkat aja:
auth: "none"dihapus di v2026.1.29 — gateway langsung exit abis upgrade- Exec approval punya dua layer — bahkan kalo lo fix satu, yang satu lagi bisa nge-blok
- Cron job auto-disable abis 3 error berturut-turut — lo baru notice 3 hari kemudian
- Session bloat — gateway melambat tanpa lo sadari
- Discord WebSocket disconnect + typing indicator nyangkut di v2026.2.24
- CVE-2026-25253 — one-click RCE via token leakage di versi lama
Lo bisa fix semua ini manual. Atau lo bisa install openclaw-ops dan tidur nyenyak.
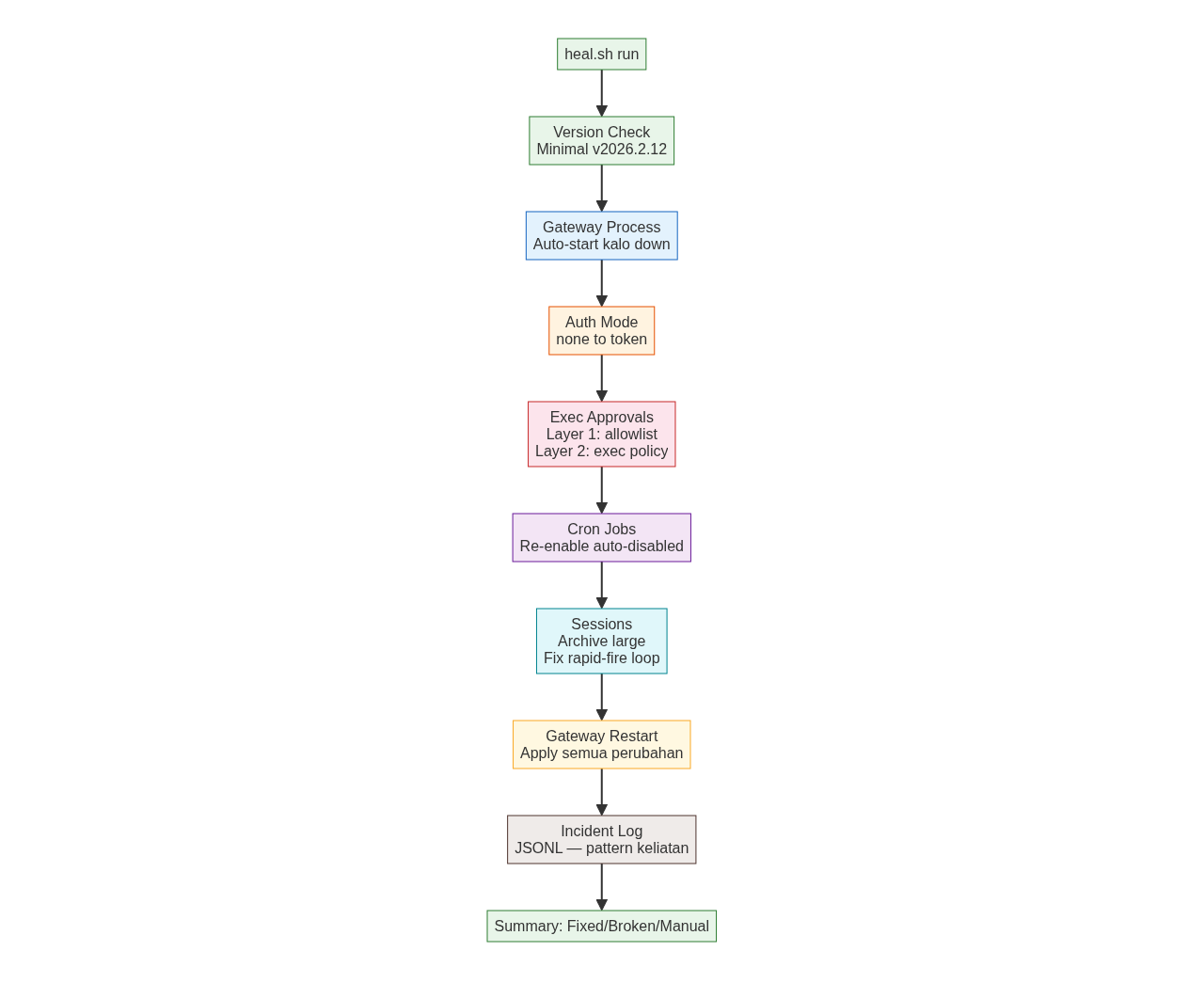
Apa Yang Di-Repair Otomatis?
Install
openclaw skills install https://github.com/cathrynlavery/openclaw-ops
cd ~/.openclaw/skills/openclaw-ops
bash scripts/heal.sh
Muncul kaya gini:
OpenClaw Self-Heal
────────────────────────────────
[1] Gateway process ✓ Running
[2] Auth config ✓ Token mode
[3] Exec approvals ✓ Layer 1 & 2 OK
[4] Cron jobs ✓ 3 jobs active
[5] Agent sessions ✓ No bloat
Summary
────────────────────────────────
✅ All checks passed — nothing to fix
Kalo ada yang break, bakal keliatan di kolom Fixed dan langsung di-repair.
Watchdog: Auto-Restart Tanpa Lo Ngapa-ngapain
heal.sh buat on-demand. Tapi kalo gateway mati jam 3 pagi?
# Linux — systemd
sudo cp scripts/openclaw-watchdog.service /etc/systemd/system/
sudo systemctl enable openclaw-watchdog
sudo systemctl start openclaw-watchdog
# macOS — LaunchAgent
ln -sf ~/.openclaw/skills/openclaw-ops/scripts/openclaw-watchdog.plist ~/Library/LaunchAgents/
launchctl load ~/Library/LaunchAgents/openclaw-watchdog.plist
NOTE: watchdog.sh bikin PID file di
/tmp/openclaw-watchdog.pid— ini yang bikin dia survives reboot di macOS.
Watchdog punya 3 tier escalation:
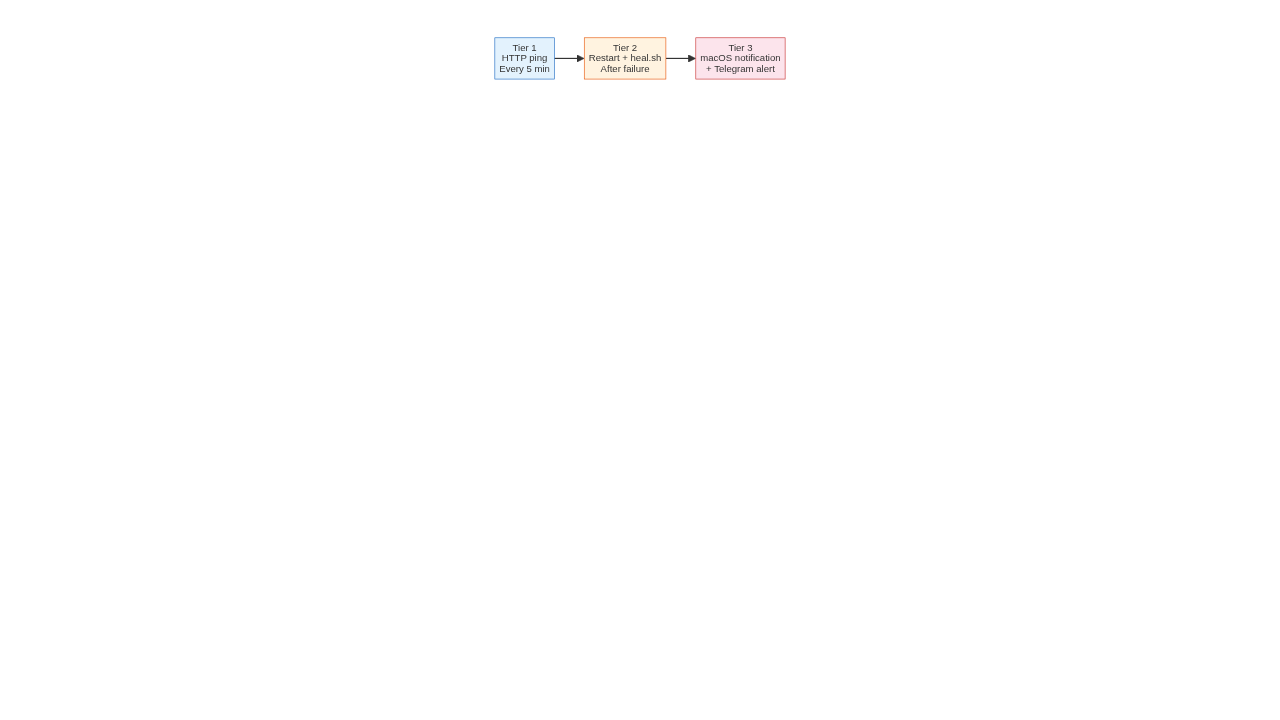
Tier 3 baru ngirim notification abis 3 kali failure berturut-turut — jadi lo gak di-spam.
Exec Approval: The Silent Killer
Ini yang paling sering bikin agents stall tapi lo gak sadar.
Dua layer independent — kedua-duanya harus bener:
Layer 1: Per-Agent Allowlist
~/.openclaw/exec-approvals.json — kalo ada agent dengan allowlist: [], dia shadow wildcard *. Gateway check agent-specific entry duluan, block semua command, gak pernah jatuh ke rule global.
Layer 2: Exec Policy Settings
Ini yang sering gak ke-notice. Even kalo allowlist udah bener, tools.exec.security bisa ke-reset ama update:
{
"allowMode": "all",
"denyPatterns": [],
"requireApproval": []
}
WARNING: Never run OpenClaw below v2026.2.12 — multiple CVEs including CVE-2026-25253 (one-click RCE) remain unpatched. Upgrade first, then run heal.sh.
Symptoms kalo ini break:
- Agent kirim
/approve allow-alwayske lo tiap 30 menit - Logs show
exec.approval.waitDecisiontimeout (1800s) - Heartbeat fails silently
- Command sederhana work, command kompleks diblok
Security Scanning: 4 Layer Defense
Pre-Install Vetting
Sebelum install skill apapun dari ClawHub:
bash scripts/skill-audit.sh openclaw-gmail-automation
# Output: LOW / MEDIUM / HIGH risk
Scan buat API keys, network calls mencurigakan, command berbahaya.
Config Hardening
bash scripts/security-scan.sh --harden
Harden config permissions, enforce exec policy, setup fail2ban.
Drift Detection
Kalo ada file skill yang diubah tanpa lo tau:
bash scripts/security-scan.sh --drift
Bikin SHA-256 baseline, compare tiap next run. Kalo ada file baru/modified/removed — lo dikasih tau.
Check Buat Update Baru
Abis OpenClaw update, jalankan:
bash scripts/check-update.sh
Ntar dia compare versi sekarang vs sebelumnya, explain apa yang break, dan kalo ada fix available, tunjukin apa yang perlu dirubah di config.
Logs: Incident History
Tiap heal run menulis ke JSONL:
cat ~/.openclaw/logs/heal-incidents.jsonl | python3 -m json.tool
{
"ts": "2026-04-03T02:00:00Z",
"outcome": "fixed",
"fixed": [
"Cron re-enabled: email-digest",
"Exec approval wildcard added for: raka"
],
"broken": [],
"manual": []
}
Abis 1 bulan, lo bisa lihat pattern — "cron email-digest keeps disabling" atau "setiap abis update, exec approval ke-reset". Berguna banget buat debugging.
Yang Lo Perlu Paham
- Minimum version: v2026.2.12 — kalo lo di bawah ini, upgrade dulu. Banyak CVE yang udah di-patch.
- Node.js v22+ — bukan Bun. Bun cause WhatsApp/Telegram issues.
- Dua layer exec approval — lo bisa fix Layer 1, tapi Layer 2 tetep bisa nge-blok.
- Watchdog auto-restart — ini bukan replacement buat monitoring. Ini insurance.
- Version check tiap heal — kalo versi berubah, heal.sh kasih tau apa yang perlu di-check.
Referensi
Skill ini dari cathrynlavery/openclaw-ops. Credit ke Cathryn Lavery dan contributors.
Script yang dipake:
- heal.sh — one-shot auto-fix
- watchdog.sh — 5-minute guardian
- security-scan.sh — hardening + drift + credentials
- skill-audit.sh — pre-install vetting
- check-update.sh — version change detector
OpenClaw Sumopod — Self-Healing Gateway as a Service
Want this self-healing setup running on your own VPS 24/7 without managing it yourself?
OpenClaw Sumopod provides:
- Pre-configured self-healing scripts
- 24/7 monitoring and auto-restart
- Security hardening built-in
- Weekly health reports to Telegram
Get started: https://blog.fanani.co/sumopod
Butuh bantuan setup OpenClaw, konsultasi IT, atau mau diskusi project engineering? Book a call langsung — gratis.
Book a Call — Gratis via Cal.com — WITA (UTC+8)
Ada Pertanyaan? Yuk Ngobrol!
Butuh bantuan setup OpenClaw, konsultasi IT, atau mau diskusi project engineering? Book a call langsung — gratis.
Book a Call — Gratisvia Cal.com • WITA (UTC+8)
📬 Subscribe Newsletter
FreeDapat alert setiap ada artikel baru langsung ke inbox kamu. Free, no spam. 🚀
👥 Join 0+ engineers & tech enthusiasts
Zainul Fanani
Founder, Radian Group. Engineering & tech enthusiast.

💬 Komentar